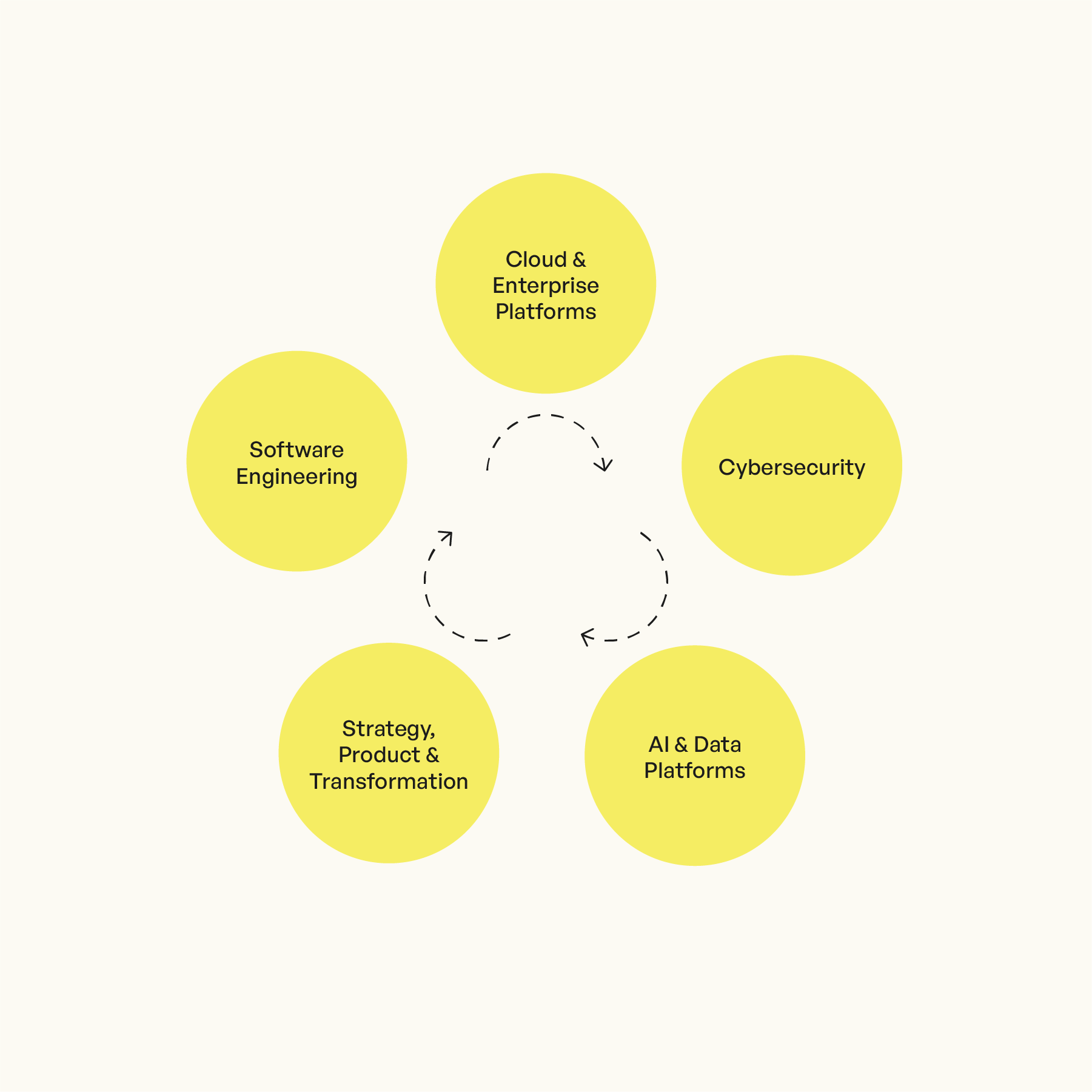
We Help You Build the Foundation for ISO 27001 Compliance
Mobilidée partnered with us to formalize their information security approach and achieve ISO 27001 certification. Combining strategic guidance with Smartcockpit, we automated governance, improved team awareness, and built a long-term compliance framework.
“Cybersecurity is neverending. With the right mindset and tools, we can stay ahead of the threats—and ISO 27001 gave us the right foundation.”
– Giorgio Giovannini, Founder